Code:
http://fileups.net/file/0vey8
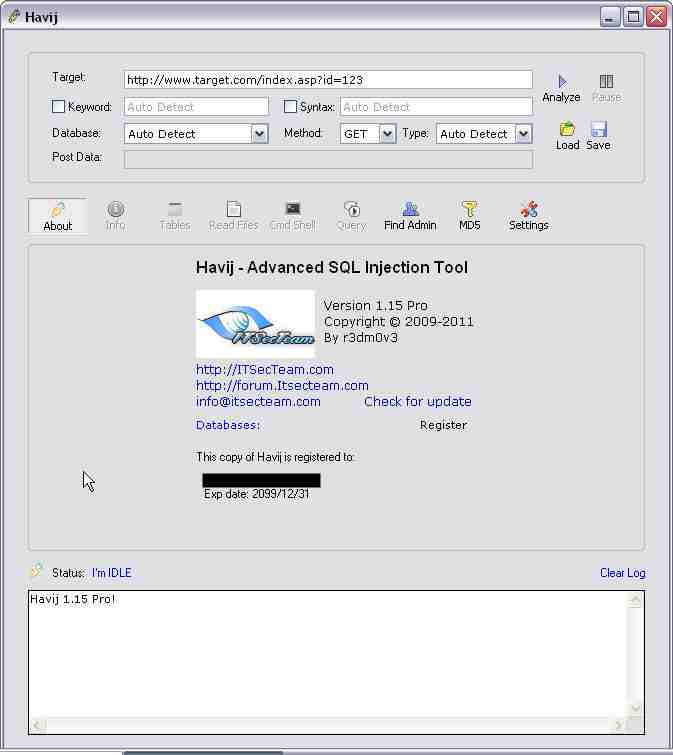
Havij can take advantage of a vulnerable web application. By using this software user can perform back-end database fingerprint, retrieve DBMS users and password hashes, dump tables and columns, fetching data from the database, running SQL statements and even accessing the underlying file system and executing commands on the operating system.
The power of Havij that makes it different from similar tools is its injection methods. The success rate is more than 95% at injectiong vulnerable targets using Havij. The user friendly GUI (Graphical User Interface) of Havij and automated settings and detections makes it easy to use for everyone even amateur users.
Havij supports following databases and injection methods.
* MsSQL with error: Microsoft SQL Server injection using error based method
* MsSQL no error: Microsoft SQL Server injection using union
* MsSQL Blind: Microsoft SQL Server injection using blind method
* MySQL unknown ver: MySQL injection using union
* MySQL Blind: MySQL injection using blind method
* MySQL error based: MySQL injection using error based method
* Oracle: Oracle injection using union method
* PostgreSQL: PostgreSQL injection using union method
* MsAccess: Microsoft Access injection using union method
* MsAccess Blind: Microsoft Access injection using blind method
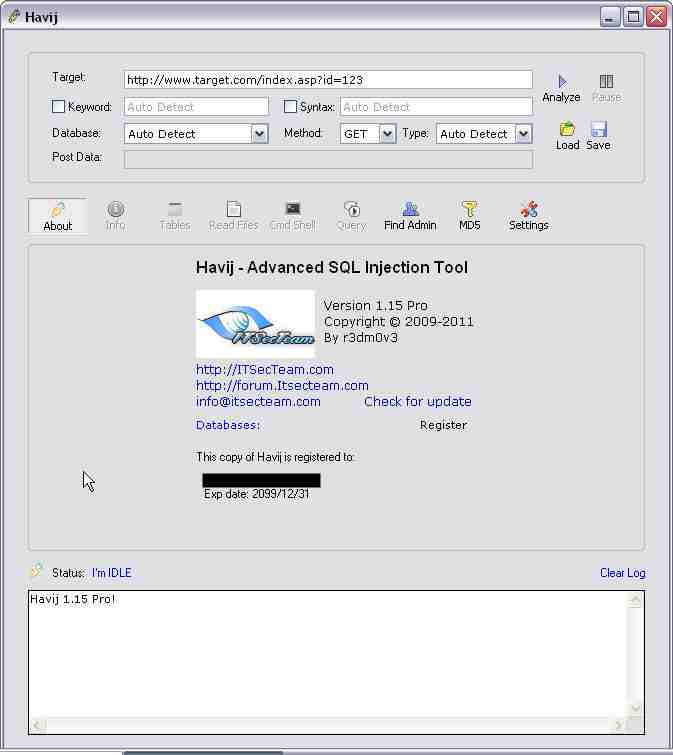











 Advance SQL Injection Tool - Portable Havij ful
Advance SQL Injection Tool - Portable Havij ful




 Reply With Quote
Reply With Quote






Bookmarks